It’s been estimated that over 90% of malicious threats use DNS to some degree.
What is DNS Filtering?
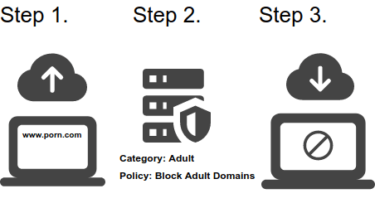
DNS Filtering analyzes DNS requests made on your network and takes action to allow or block such requests based on policy. It works by having a recursive DNS server with added functionality to understand configured polices, recognize domains based on categories, and then present a block page when a domain is not allowed. This block functionality is referred to as a DNS Sinkhole and functions like this:
- Client requests xyz.com
- Recursive Resolver determines xyz.com is blocked due to policy rules
- Recursive resolver spoofs xyz.com and shows a block page response.
DNS filters are sometimes referred to as DNS firewalls or DNS RPZ (response policy zone).
What Can DNS Filtering do?
Content Filtering: able to recognize domains based on categories such as pornography, hate speech, illegal activities, copyright downloads, etc. It can even enforce safe search with popular search engines.
Email/Phishing Defense: can supplement your existing email and spam protections by acting as an additional layer to stop phishing URLs and limit any damage that might slip through.
Malware Defense: can identify botnet and command and control domains associated with ransomware, spyware, and other malicious intent preventing this activity.
Data Exfiltration Defense: Some data exfiltration uses the DNS channel as a method to bypass endpoint and firewall protections tricking them into letting what seems like harmless DNS traffic leak out. DNS filtering can identify this activity and block offending connections.
IoT Protection: When protecting headless devices such as IoT that use DNS near exclusively to communicate with resources, DNS filtering provides ideal protection where the installation of endpoint software is not possible.
Advantages
DNS filtering by nature has a number of advantages. For one, it deals at the very first layer of cyber-defense, outside your perimeter in the cloud. It is relatively inexpensive compared to other measures adding almost no latency with no network or hardware resource load and no client side agents required for on-premise network protection. As a result, the ongoing cost to operate and maintain is very attractive. Additionally with more of the internet operating via HTTPS, DNS layer filtering requires no man-in-the-middle. Most solutions offer networkwide setup in minutes.
When acting as a primary content filter, DNS filtering is more than capable of fulfilling content obligations associated with requirements like CIPA, Child Information and Protection Act.
Disadvantages
DNS filtering cannot filter IP only network connections as there are no DNS requests to examine. DNS filtering does not replace firewalls for network port and IP level protections.
The Power of Layers
Proper network security is configured in terms of layers. What one tool on one layer might miss, another might catch. The more layers you have, the less likely threats are going to get through. Combined with firewalls, email protection, and endpoint protection, DNS filtering offers a solid first line defense for internet connected devices.