Freelance researcher Xavier Mertens discovered malware using a more detailed location service than previous types. For some time now, malicious software has queried IP data in order to determine if an infected victim was within a desired country or even a specific organization that was to be targeted. With this newer sample, the malware makes use of an API service that serves up detailed location data based on the last known location of a routers MAC address.
What does greater location accuracy help with?
For one, an attacker could better understand how their malware was spreading amongst related networks. It could also be used to better ID a specific branch location of a target for instance.
More details?
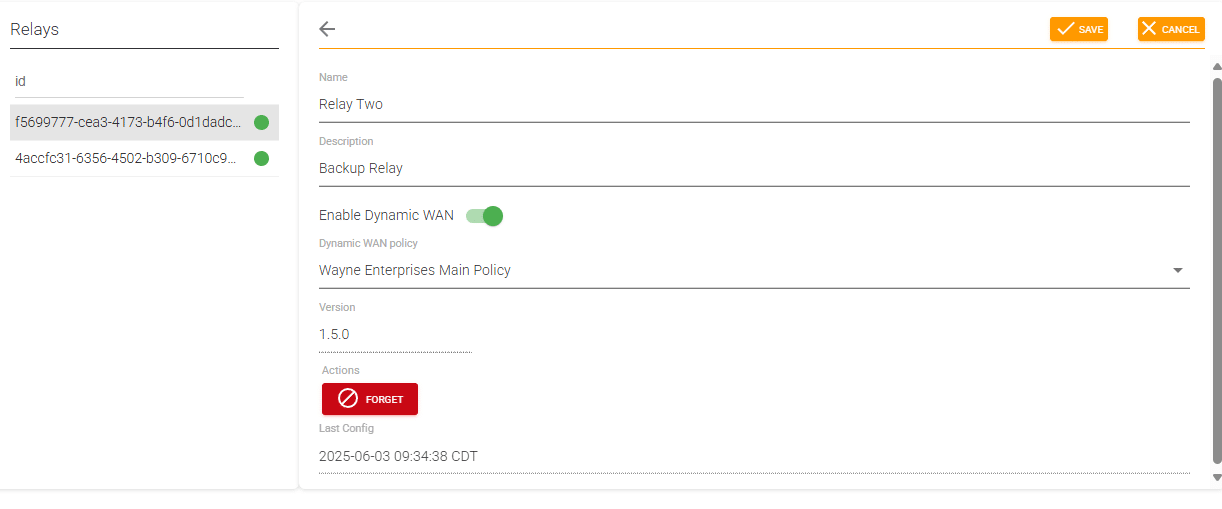
Alexander’s post goes into greater detail based on his observed sample. For ScoutDNS users, we pay special attention to domain based indicators.
Domain Indicators:
We can defend against malware with DNS filtering. We usually do this by blocking command and control domains. In this case, we could block the related API service if we have no use for it, or we can simply use it to search for any networks that have tried to access it.
icanhazip.com (domain used to retrieve WAN IP address)
api.mylnikov.org (API of the MAC address call service)
ScoutDNS makes it easy for organizations to quickly search across any number of networks and locations to find potentially malicious activity.