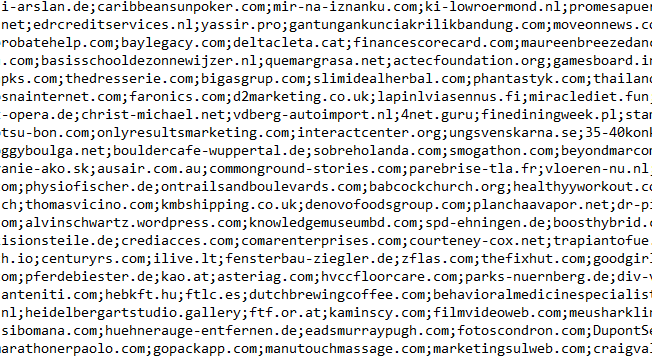
The number of infected devices and networks from the Kaseya REvil supply chain attack continue to mount. We have parsed out the complete list of domains marked as Command and Control from the decrypted JSON config file provided by Fabian Woser.
There are 1223 domains listed in the file. Keep in mind, we cannot confirm that any or all of these hosts are compromised at this time, they are simply pulled from the REvil malware configuration file.
These domains were only recently made aware to the community after the fact. As a result, many were likely not marked as malicious prior. ScoutDNS customers can use domain search to check the past 30 days for any hits from this list.
Is your domain on this list?
If you can verify that your domain/server is not compromised let us know and we may release a second list of sanitized/safe domains.
Cleared Domains
Download the list of previously reported but now cleared domains here.